# 经验分享
# JXWAF 节点自定义端口部署
# Docker 部署(推荐)
docker run -p 80:80 -p 443:443 -e TZ=Asia/Shanghai -e JXWAF_SERVER='you jxwaf server url ' -e WAF_AUTH='your key' -e HTTP_PORT=80 -e HTTPS_PORT=443 jxwaf/jxwaf:latest
配置变量说明:
JXWAF_SERVER
jxwaf 控制台服务器地址,这里为 http://demo.jxwaf.com:8000 ,注意,地址不需要带路径,即 http://demo.jxwaf.com:8000/ 是错误输入
WAF_AUTH
jxwaf 控制台中 系统配置 -> 基础信息 中 waf_auth 的值
HTTP_PORT
http 端口
HTTPS_PORT
https 端口
例子:
在 8000 端口部署 HTTP 服务
docker run -p 8000:8000 -d -e TZ=Asia/Shanghai -e JXWAF_SERVER='http://demo.jxwaf.com:8000' -e WAF_AUTH='ee747988-612b-4790-b8ea-fb49c04fc1ea' -e HTTP_PORT=8000 jxwaf/jxwaf:latest
在 8002 端口部署 HTTPS 服务
docker run -p 8002:8002 -d -e TZ=Asia/Shanghai -e JXWAF_SERVER='http://demo.jxwaf.com:8000' -e WAF_AUTH='ee747988-612b-4790-b8ea-fb49c04fc1ea' -e HTTPS_PORT=8002 jxwaf/jxwaf:latest
# Docker Compose 部署
services:
jxwaf_base:
image: "jxwaf/jxwaf:latest"
ports:
- "80:80"
- "443:443"
environment:
HTTP_PORT: 80
HTTPS_PORT: 443
JXWAF_SERVER: you_jxwaf_server_url
WAF_AUTH: you_auth_key
TZ: Asia/Shanghai
restart: unless-stopped
docker-compose.yml 配置文件说明:
JXWAF_SERVER
jxwaf 控制台服务器地址,这里为 http://demo.jxwaf.com:8000 ,注意,地址不需要带路径,即 http://demo.jxwaf.com:8000/ 是错误输入
WAF_AUTH
jxwaf 控制台中 系统配置 -> 基础信息 中 waf_auth 的值
HTTP_PORT
http 端口
HTTPS_PORT
https 端口
例子:
在 8000 端口部署 HTTP 服务
services:
jxwaf_base:
image: "jxwaf/jxwaf:latest"
ports:
- "8000:8000"
environment:
HTTP_PORT: 8000
JXWAF_SERVER: http://demo.jxwaf.com:8000
WAF_AUTH: ee747988-612b-4790-b8ea-fb49c04fc1ea
TZ: Asia/Shanghai
restart: unless-stopped
在 8002 端口部署 HTTPS 服务
services:
jxwaf_base:
image: "jxwaf/jxwaf:latest"
ports:
- "8002:8002"
environment:
HTTPS_PORT: 8002
JXWAF_SERVER: http://demo.jxwaf.com:8000
WAF_AUTH: ee747988-612b-4790-b8ea-fb49c04fc1ea
TZ: Asia/Shanghai
restart: unless-stopped
# 控制台新增网站配置
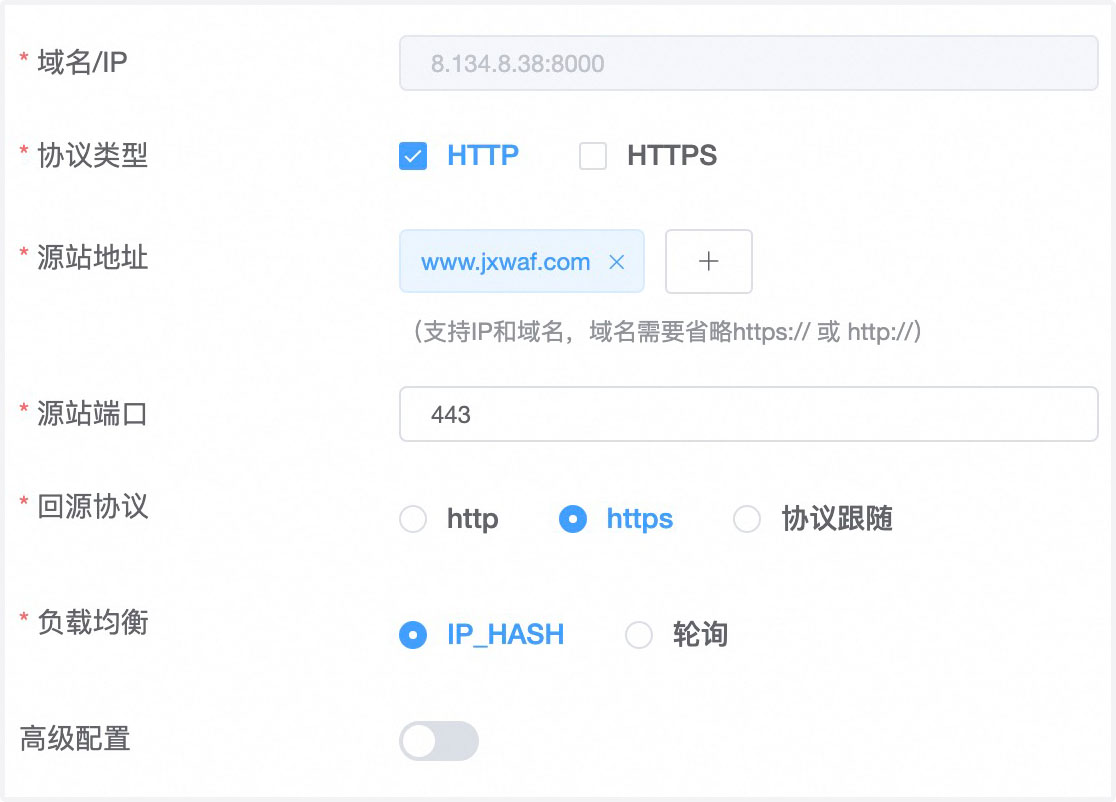
相比于正常的域名配置,比如 demo.jxwaf.com,自定义端口部署,则需要配置为demo.jxwaf.com:8000,直接在需要配置自定义端口的网站地址后面加上端口即可。
# CC防护的JS文件独立部署
默认情况下,CC防护功能中引用的js文件是在域名 cc.jxwaf.top 下面,域名通过CloudFare提供服务。如果需要独立部署在其他CDN上,可以参考下面进行配置。
# JS文件独立部署
JS文件在 https://github.com/jx-sec/jxwaf-mini-server 中的 cc_js.zip,下载后发布到CDN上即可
# Docker启动容器配置
docker run -p 80:80 -p 443:443 -e JXWAF_SERVER='you jxwaf server url ' -e WAF_AUTH='your key' -e HTTP_PORT=80 -e HTTPS_PORT=443 -e WAF_CC_JS_WEBSITE='https://cc.jxwaf.top/' jxwaf/jxwaf:latest
配置变量说明:
WAF_CC_JS_WEBSITE
指定CC文件来源网站,这里需要带上路径,即 "https://cc.jxwaf.top/" 是正确输入,"https://cc.jxwaf.top" 是错误输入
# Docker Compose启动容器配置
services:
jxwaf_base:
image: "jxwaf/jxwaf:latest"
ports:
- "80:80"
- "443:443"
environment:
HTTP_PORT: 80
HTTPS_PORT: 443
JXWAF_SERVER: you_jxwaf_server_url
WAF_AUTH: you_auth_key
TZ: Asia/Shanghai
WAF_CC_JS_WEBSITE: https://cc.jxwaf.top/
restart: unless-stopped
docker-compose.yml 配置文件说明:
WAF_CC_JS_WEBSITE
指定CC文件来源网站,这里需要带上路径,即 "https://cc.jxwaf.top/" 是正确输入,"https://cc.jxwaf.top" 是错误输入
# 源代码部署配置
配置文件: /opt/jxwaf/nginx/conf/jxwaf/jxwaf_config.json
配置文件内容为json格式,修改 waf_cc_js_website 的值即可
默认值为 "https:\/\/cc.jxwaf.top\/" ,修改的时候要注意json字符串转义,例如新的域名是 cc.test.com,则 正确的字符串应该为 "https:\/\/cc.test.top\/"
# CC攻击网络层封禁
# 节点服务器部署jxwaf_ipset_block
# yum install -y ipset
# ipset create blacklist hash:ip hashsize 65535 maxelem 1000000 timeout 86400
# iptables -I INPUT -m set --match-set blacklist src -j DROP
# iptables -I FORWARD -m set --match-set blacklist src -j DROP
# git clone https://github.com/jx-sec/jxwaf.git
# cd jxwaf/ipset_block
# chmod +x jxwaf_ipset_block
# nohup ./jxwaf_ipset_block -auth aaaa -port 6677 &
# curl 127.0.0.1:6677/banip -d '{"network_block_ip":"1.1.1.1","auth":"aaaa"}'
# ipset list
命令说明:
1、安装IPSet
yum install -y ipset
这步安装IPSet,一个用于管理IP地址集合和使用这些集合进行网络过滤、转发决策的工具。
2、配置IPSet和Iptables以阻止恶意IP
ipset create blacklist hash:ip hashsize 65535 maxelem 1000000 timeout 86400
iptables -I INPUT -m set --match-set blacklist src -j DROP
iptables -I FORWARD -m set --match-set blacklist src -j DROP
这里首先创建了一个名为blacklist的IPSet集合,用来存储需要被阻止的IP地址。然后通过iptables将所有在这个集合中的IP地址发送的包都丢弃,在INPUT(处理进入本机数据包)和FORWARD(处理转发数据包)链上插入这些规则。集合的过期时间是一天,最多100万条数据。
3、部署和运行jxwaf_ipset_block
git clone https://github.com/jx-sec/jxwaf.git
cd jxwaf/ipset_block
chmod +x jxwaf_ipset_block
nohup ./jxwaf_ipset_block -auth aaaa -port 6677 &
先克隆jxwaf的项目代码,进入到ipset_block目录,给jxwaf_ipset_block程序执行权限,然后在后台启动这个应用,它监听6677端口,并设置了认证用的关键字aaaa。
4、通过API调用更新防火墙规则
curl 127.0.0.1:6677/banip -d '{"network_block_ip":"1.1.1.1","auth":"aaaa"}'
ipset list
这个是验证步骤。通过向jxwaf_ipset_block运行的服务发送POST请求,使用之前设置的认证关键字aaaa,请求阻止IP地址1.1.1.1。这条命令实现了对特定IP地址的动态封禁。通过ipset list可以查看封禁的结果。
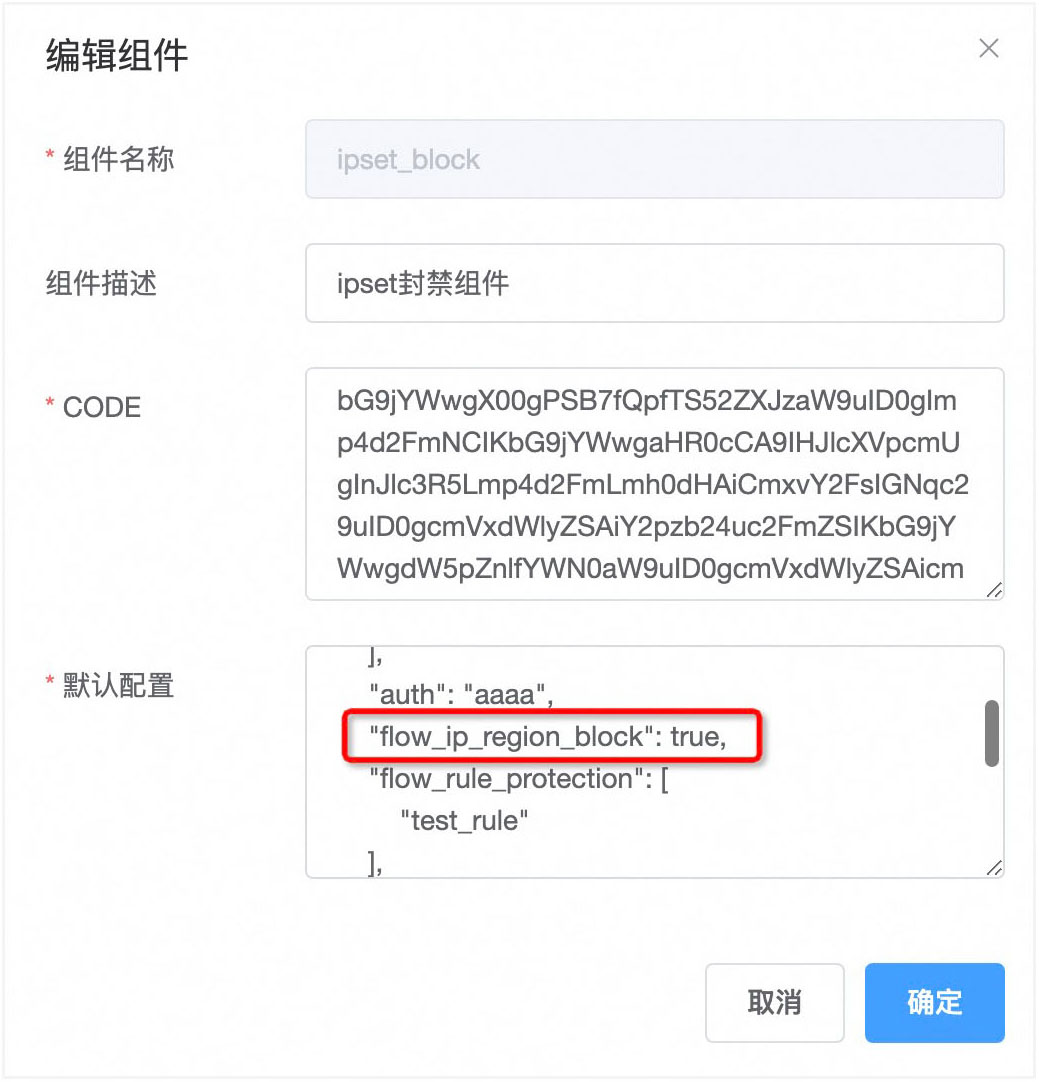
# JXWAF控制台新建ipset_block组件
JXWAF控制台 -> 防护管理 -> 分析组件 -> 新建组件
- 组件名称
ipset_block
- 组件描述
ipset封禁组件
- CODE
bG9jYWwgX00gPSB7fQpfTS52ZXJzaW9uID0gImp4d2FmNCIKbG9jYWwgaHR0cCA9IHJlcXVpcmUgInJlc3R5Lmp4d2FmLmh0dHAiCmxvY2FsIGNqc29uID0gcmVxdWlyZSAiY2pzb24uc2FmZSIKbG9jYWwgdW5pZnlfYWN0aW9uID0gcmVxdWlyZSAicmVzdHkuanh3YWYudW5pZnlfYWN0aW9uIgoKbG9jYWwgZnVuY3Rpb24gc2VuZF9pcHNldF9ibG9jayhwZXJpb2QsaXBfYmFuX3NlcnZlcixibGFja19pcCxpcF9iYW5fYXV0aCkKICBsb2NhbCBpcF9iYW5fd2Vic2l0ZSA9ICJodHRwOi8vIi4uaXBfYmFuX3NlcnZlci4uIi9iYW5pcCIKICBsb2NhbCBodHRwYyA9IGh0dHAubmV3KCkKICBodHRwYzpzZXRfdGltZW91dHMoMTAwMDAsIDEwMDAwLCAxMDAwMCkKICBsb2NhbCBib2R5X2RhdGEgPSB7CiAgICBuZXR3b3JrX2Jsb2NrX2lwID0gIGJsYWNrX2lwLAogICAgYXV0aCA9IGlwX2Jhbl9hdXRoCiAgfQogIGxvY2FsIHJlcywgZXJyID0gaHR0cGM6cmVxdWVzdF91cmkoIGlwX2Jhbl93ZWJzaXRlICwgewogICAgbWV0aG9kID0gIlBPU1QiLAogICAgaGVhZGVycyA9IHsKICAgICAgWyJDb250ZW50LVR5cGUiXSA9ICJhcHBsaWNhdGlvbi9qc29uO2NoYXJzZXQ9VVRGLTgiLAogICAgfSwKICAgIGJvZHkgPSBjanNvbi5lbmNvZGUoYm9keV9kYXRhKQogIH0pCiAgaWYgbm90IHJlcyB0aGVuCiAgICBuZ3gubG9nKG5neC5FUlIsInNlbmQgaHR0cCBmYWlsZWQgdG8gcmVxdWVzdDogIiwgZXJyKQogICAgcmV0dXJuIAogIGVuZAogIGlmIHJlcy5zdGF0dXMgfj0gMjAwIHRoZW4KICAgIG5neC5sb2cobmd4LkVSUiwgIklQIGJhbiByZXF1ZXN0IHJldHVybmVkIG5vbi0yMDAgcmVzcG9uc2U6ICIsIHJlcy5zdGF0dXMpCiAgICByZXR1cm4KICBlbmQKICBsb2NhbCByZXNfYm9keSA9IGNqc29uLmRlY29kZShyZXMuYm9keSkKICBpZiBub3QgcmVzX2JvZHkgdGhlbgogICAgbmd4LmxvZyhuZ3guRVJSLCJzZW5kICBmYWlsLGZhaWxlZCB0byBkZWNvZGUgcmVzcCBib2R5IikKICAgIG5neC5sb2cobmd4LkVSUixyZXMuYm9keSkKICAgIHJldHVybgogIGVuZAogIGlmIHJlc19ib2R5WydyZXN1bHQnXSB+PSB0cnVlIHRoZW4KICAgIG5neC5sb2cobmd4LkVSUiwicmVzdWx0IH49IHRydWUgIiApCiAgICBuZ3gubG9nKG5neC5FUlIscmVzLmJvZHkpCiAgICByZXR1cm4KICBlbmQKICByZXR1cm4gdHJ1ZQplbmQKCmZ1bmN0aW9uIF9NLmNoZWNrKGNvbmZfZGF0YSkKICBpZiBjb25mX2RhdGEgPT0gbmlsIHRoZW4KICAgIHJldHVybiAKICBlbmQKCiAgbG9jYWwganh3YWZfaXBzZXRfbm9kZSA9ICBjb25mX2RhdGFbJ2p4d2FmX2lwc2V0X25vZGUnXQogIGlmIHR5cGUoanh3YWZfaXBzZXRfbm9kZSkgfj0gJ3RhYmxlJyAgdGhlbgogICAgcmV0dXJuCiAgZW5kCgogIGxvY2FsIGF1dGggPSBjb25mX2RhdGFbJ2F1dGgnXQogIGlmIHR5cGUoYXV0aCkgfj0gJ3N0cmluZycgIHRoZW4KICAgIHJldHVybgogIGVuZAoKICBsb2NhbCBmbG93X2lwX3JlZ2lvbl9ibG9jayA9IGNvbmZfZGF0YVsnZmxvd19pcF9yZWdpb25fYmxvY2snXQogIGlmIHR5cGUoZmxvd19pcF9yZWdpb25fYmxvY2spIH49ICdib29sZWFuJyAgdGhlbgogICAgbmd4LmxvZyhuZ3guRVJSLHR5cGUoZmxvd19pcF9yZWdpb25fYmxvY2spKQogICAgcmV0dXJuCiAgZW5kCgogIGxvY2FsIGZsb3dfcnVsZV9wcm90ZWN0aW9uID0gY29uZl9kYXRhWydmbG93X3J1bGVfcHJvdGVjdGlvbiddCiAgaWYgdHlwZShmbG93X3J1bGVfcHJvdGVjdGlvbikgfj0gJ3RhYmxlJyAgdGhlbgogICAgcmV0dXJuCiAgZW5kCiAgbG9jYWwgZmxvd19lbmdpbmVfcHJvdGVjdGlvbiA9IGNvbmZfZGF0YVsnZmxvd19lbmdpbmVfcHJvdGVjdGlvbiddCiAgaWYgdHlwZShmbG93X2VuZ2luZV9wcm90ZWN0aW9uKSB+PSAndGFibGUnICB0aGVuCiAgICByZXR1cm4KICBlbmQKCiAgbG9jYWwgZmxvd19pcF9yZWdpb25fYmxvY2tfcmVzdWx0ID0gbmd4LmN0eC5mbG93X2lwX3JlZ2lvbl9ibG9ja19yZXN1bHQKICBsb2NhbCBmbG93X3J1bGVfcHJvdGVjdGlvbl9yZXN1bHQgPSBuZ3guY3R4LmZsb3dfcnVsZV9wcm90ZWN0aW9uX3Jlc3VsdAogIGxvY2FsIGZsb3dfZW5naW5lX3Byb3RlY3Rpb25fcmVzdWx0ID0gbmd4LmN0eC5mbG93X2VuZ2luZV9wcm90ZWN0aW9uX3Jlc3VsdAogIGxvY2FsIGNoZWNrX3Jlc3VsdCAKICBpZiAgZmxvd19pcF9yZWdpb25fYmxvY2sgPT0gdHJ1ZSBhbmQgZmxvd19pcF9yZWdpb25fYmxvY2tfcmVzdWx0IHRoZW4KICAgIGNoZWNrX3Jlc3VsdCA9IHRydWUKICBlbmQKCiAgZm9yIF8sdiBpbiBpcGFpcnMoZmxvd19ydWxlX3Byb3RlY3Rpb24pIGRvIAogICAgaWYgZmxvd19ydWxlX3Byb3RlY3Rpb25fcmVzdWx0W3ZdIHRoZW4KICAgICAgY2hlY2tfcmVzdWx0ID0gdHJ1ZQogICAgZW5kCiAgZW5kCgogIGZvciBfLHYgaW4gaXBhaXJzKGZsb3dfZW5naW5lX3Byb3RlY3Rpb24pIGRvIAogICAgaWYgZmxvd19lbmdpbmVfcHJvdGVjdGlvbl9yZXN1bHRbdl0gdGhlbgogICAgICBjaGVja19yZXN1bHQgPSB0cnVlCiAgICBlbmQKICBlbmQKCiAgaWYgY2hlY2tfcmVzdWx0IHRoZW4KICAgIGxvY2FsIHNyY19pcCA9IG5neC5jdHguc3JjX2lwIG9yIG5neC52YXIucmVtb3RlX2FkZHIKICAgIGZvciBfLHYgaW4gaXBhaXJzKGp4d2FmX2lwc2V0X25vZGUpIGRvCiAgICAgIGxvY2FsIG9rLCBlcnIgPSBuZ3gudGltZXIuYXQoMCxzZW5kX2lwc2V0X2Jsb2NrLHYsc3JjX2lwLGF1dGgpCiAgICAgIGlmIG5vdCBvayB0aGVuCiAgICAgICAgaWYgZXJyIH49ICJwcm9jZXNzIGV4aXRpbmciIHRoZW4KICAgICAgICAgIG5neC5sb2cobmd4LkVSUiwgImZhaWxlZCB0byBjcmVhdGUgdGhlIHNlbmQgc2VuZF9pcHNldF9ibG9jayBodHRwIHRpbWVyOiAiLCBlcnIpCiAgICAgICAgZW5kCiAgICAgIGVuZAogICAgZW5kCiAgICBsb2NhbCB3YWZfbG9nID0gbmd4LmN0eC53YWZfbG9nIAogICAgd2FmX2xvZ1snd2FmX2FjdGlvbiddID0gImlwc2V0X2Jsb2NrIgogICAgbmd4LmN0eC53YWZfbG9nID0gd2FmX2xvZwogICAgdW5pZnlfYWN0aW9uLnJlamVjdF9yZXNwb25zZSgpCiAgICByZXR1cm4gdHJ1ZQogIGVuZAogIHJldHVybiAKZW5kCgpyZXR1cm4gX00=
- 默认配置
{"jxwaf_ipset_node":["1.1.1.1:6677","2.2.2.2:6677"],"auth":"aaaa","flow_ip_region_block":true,"flow_rule_protection":["test_rule"],"flow_engine_protection":["high_freq_cc_rate_check","high_freq_cc_count_check"]}
说明:
详细配置说明需要查看 组件分享 -> ipset_block组件 文档,请勿直接复制配置使用。
# 开启网络层封禁
# 开启IP区域网络层封禁
设置 执行动作 为观察模式
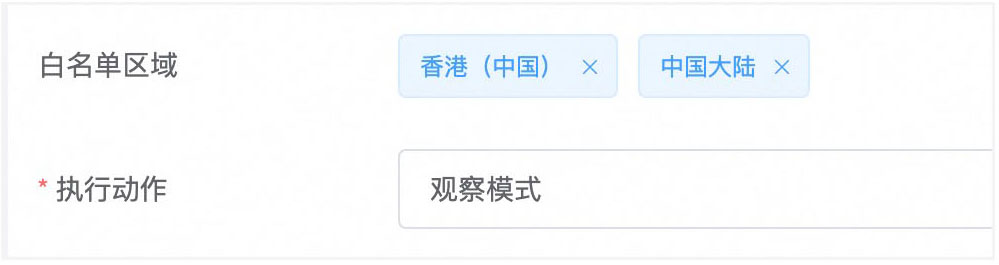
ipset_block 组件配置中 flow_ip_region_block 设置 为 true
以下是仅开启IP区域封禁情况下的配置
{"jxwaf_ipset_node":["111.230.13.94:6677"],"auth":"aaaa","flow_ip_region_block":true,"flow_rule_protection":[],"flow_engine_protection":[]}
# 开启流量防护规则网络层封禁
新建一个规则,名字为ua_cc_ipset_black,将规则的执行动作设置为观察模式
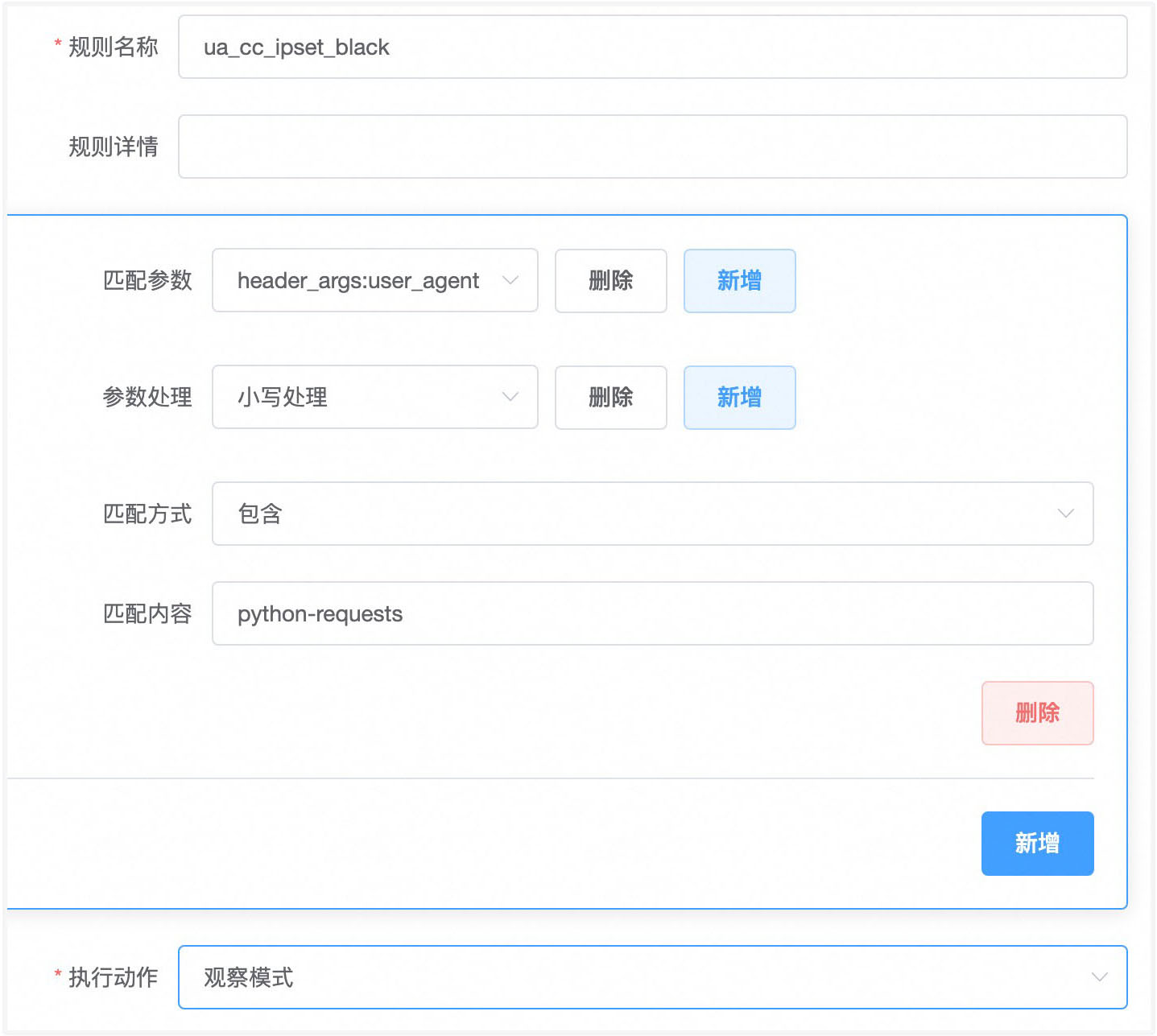
ipset_block 组件配置中 flow_rule_protection 设置为 ["ua_cc_ipset_black"]
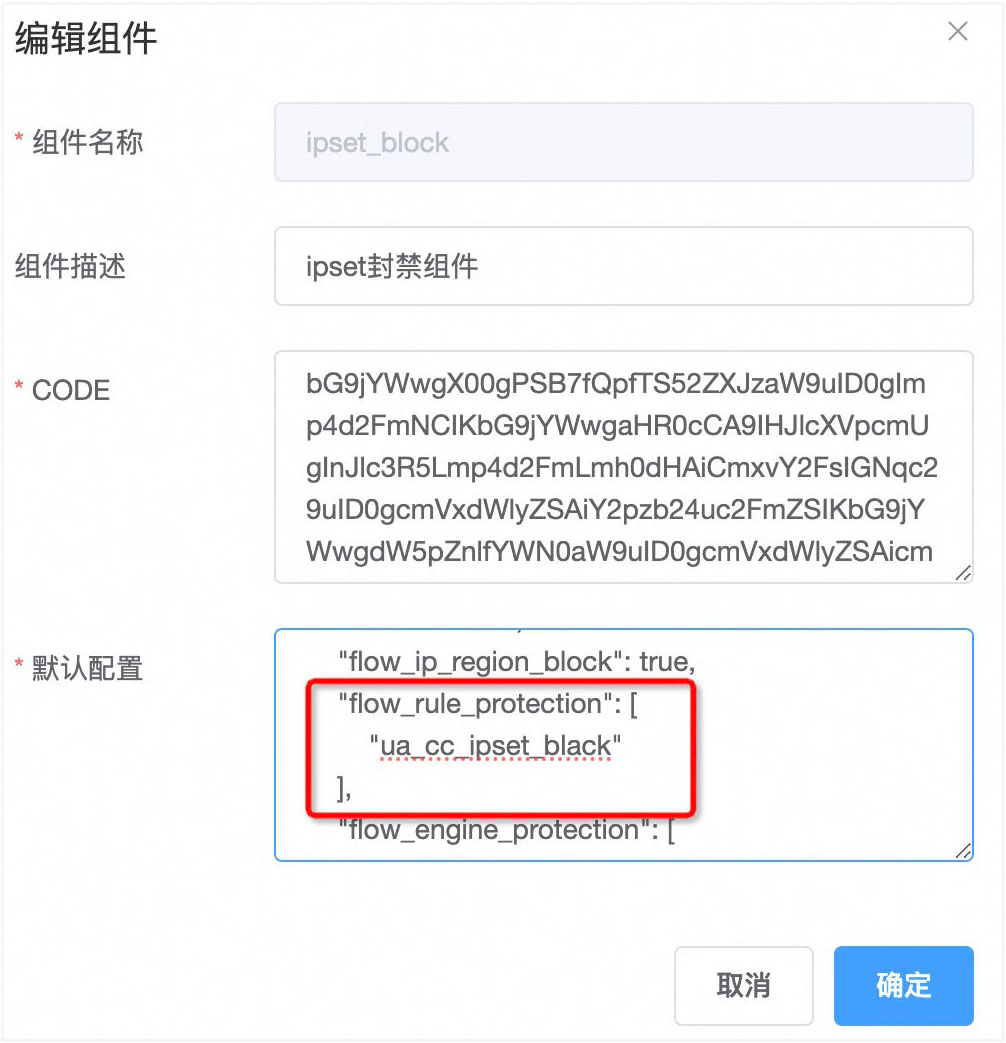
以下是仅开启流量防护规则情况下的配置
{"jxwaf_ipset_node":["111.230.13.94:6677"],"auth":"aaaa","flow_ip_region_block":false,"flow_rule_protection":["ua_cc_ipset_black"],"flow_engine_protection":[]}
如果有多条规则需要开启,例如还有规则"ua_cc_ipset_black2","ua_cc_ipset_black3",则配置为
{"jxwaf_ipset_node":["111.230.13.94:6677"],"auth":"aaaa","flow_ip_region_block":false,"flow_rule_protection":["ua_cc_ipset_black","ua_cc_ipset_black2","ua_cc_ipset_black3"],"flow_engine_protection":[]}
# 开启流量防护引擎网络层封禁
开启高频CC攻击防护网络层封禁
分别将IP请求频率检测和IP请求次数检测的执行动作设置为观察模式

ipset_block 组件配置中 flow_engine_protection 设置为 ["high_freq_cc_rate_check","high_freq_cc_count_check"]
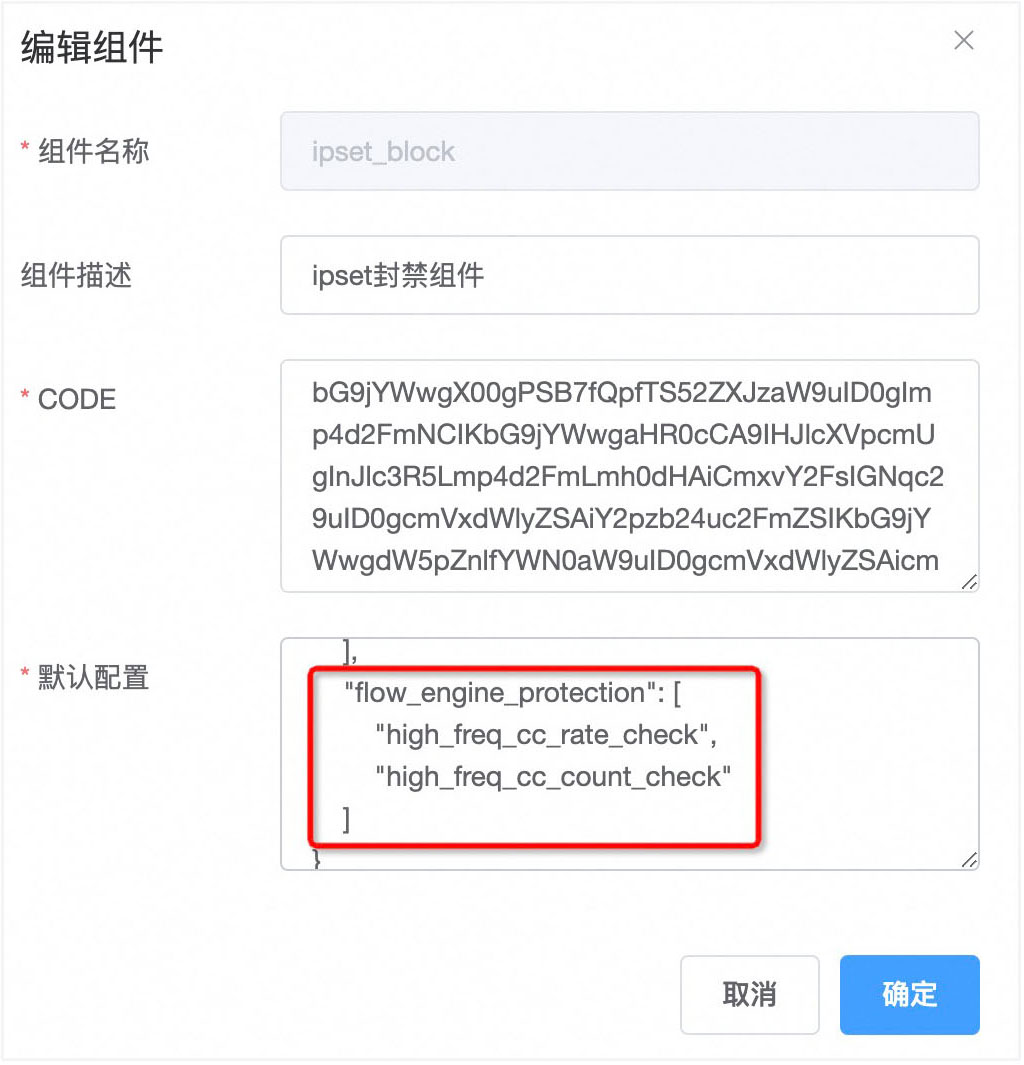
以下是仅开启IP请求频率检测和IP请求次数检测情况下的配置
{"jxwaf_ipset_node":["111.230.13.94:6677"],"auth":"aaaa","flow_ip_region_block":false,"flow_rule_protection":[],"flow_engine_protection":["high_freq_cc_rate_check","high_freq_cc_count_check"]}
流量防护引擎配置对应的值为:
high_freq_cc_rate_check
高频CC攻击防护-IP请求频率检测
high_freq_cc_count_check
高频CC攻击防护-IP请求次数检测
slow_cc_ip_count_check
慢速CC攻击防护-请求IP数量检测
slow_cc_domain_check
慢速CC攻击防护-回源保护机制
emergency_mode_check
无差别紧急防护
具体详情,请查看 组件分享 -> ipset_block组件 文档
# 实战预案
实战情况下,建议可以先把ipset_block组件中,相关的配置都开启,然后将组件状态设置为关闭。
当发现攻击时,只需将相关防护的处置配置改为观察,然后组件状态设置为开启,即可生效。
以上面的配置案例为例,全开的配置为
{"jxwaf_ipset_node":["111.230.13.94:6677"],"auth":"aaaa","flow_ip_region_block":true,"flow_rule_protection":["ua_cc_ipset_black","ua_cc_ipset_black2","ua_cc_ipset_black3"],"flow_engine_protection":["high_freq_cc_rate_check","high_freq_cc_count_check","slow_cc_ip_count_check","slow_cc_domain_check","emergency_mode_check"]}
# 通过名单防护API批量加白IP
# 名单防护新建名单
JXWAF控制台 -> 防护管理 -> 名单防护 -> 新建名单
- 名单名称
white_ip
- 名单描述
IP白名单
- 过期时间(秒)
永久生效
- 匹配参数
http_args:src_ip
- 执行动作
安全防护全加白

说明:
安全防护全加白
加白所有安全防护模块,后续检测流程中的安全防护模块都会直接跳过,不会执行检测和处置
Web 安全防护加白
加白所有 Web 安全防护模块,后续检测流程中的 Web 安全防护模块都会直接跳过,不会执行检测和处置
流量安全防护加白
加白所有流量安全防护模块,后续检测流程中的流量安全防护模块都会直接跳过,不会执行检测和处置
# API调用批量加白
# -*- coding: utf-8 -*-
import requests
import ipaddress
# API 信息
API_URL = "http://demo.jxwaf.com:8000/api/add_name_list_item"
WAF_AUTH = "ee747988-612b-4790-b8ea-fb49c04fc1ea"
NAME_LIST_NAME = "white_ip"
def add_ip_to_whitelist(ip_address):
"""
向名单添加单个 IP 地址。
"""
data = {
"waf_auth": WAF_AUTH,
"name_list_name": NAME_LIST_NAME,
"name_list_item": ip_address,
}
response = requests.post(API_URL, json=data)
# 检查响应
if response.status_code == 200:
print "Successfully added {0} to list '{1}': {2}".format(ip_address, NAME_LIST_NAME, response.json())
else:
print "Failed to add {0} to the list: {1}".format(ip_address, response.text)
def process_ip_list(ip_list):
"""
处理 IP 地址或地址段列表。
"""
for ip_input in ip_list:
try:
# 解析地址段并添加每个 IP 到名单
network = ipaddress.ip_network(unicode(ip_input), strict=False)
for ip in network:
add_ip_to_whitelist(str(ip))
except ValueError as e:
print "Error:", e
if __name__ == "__main__":
# 需要加白的IP地址
ip_list = [
"192.168.1.1",
"192.168.2.0/30", # 这将会解析并添加 192.168.2.1 至 192.168.2.2 的地址
]
process_ip_list(ip_list)
说明:
python版本为2.7,需要先运行下面命令按照依赖库
yum install python-pip
pip install requests
pip install ipaddress
修改代码中的API信息,例如控制台的地址为 1.1.1.1,waf_auth 为 aa7a7988-6a2b-4a90-a8ea-aa49c04fc1ea,名单为 white_inner_ip,则修改为
API_URL = "http://1.1.1.1:8000/api/add_name_list_item"
WAF_AUTH = "aa7a7988-6a2b-4a90-a8ea-aa49c04fc1ea"
NAME_LIST_NAME = "white_inner_ip"
之后修改代码中的 ip_list 为需要添加的IP地址,例如需要添加 10.10.1.0/24,10.0.2.3/26,则修改为
ip_list = [
"10.10.1.0/24",
"10.0.2.3/26",
]
将修改后的代码文件保存为 add_white_ip.py 运行如下命令
python add_white_ip.py
返回类似结果即为添加成功
[root@iZ7xv80j0o4igshymanzilZ tmp]# python add_white_ip.py
Successfully added 192.168.1.1 to list 'white_ip': {u'message': u'add_success', u'result': True, u'name_list_item_count': 0}
Successfully added 192.168.2.0 to list 'white_ip': {u'message': u'add_success', u'result': True, u'name_list_item_count': 0}
Successfully added 192.168.2.1 to list 'white_ip': {u'message': u'add_success', u'result': True, u'name_list_item_count': 0}
Successfully added 192.168.2.2 to list 'white_ip': {u'message': u'add_success', u'result': True, u'name_list_item_count': 0}
Successfully added 192.168.2.3 to list 'white_ip': {u'message': u'add_success', u'result': True, u'name_list_item_count': 0}
# 新增节点默认配置
# 场景说明
当一个网站对应大量域名的时候,或者网站域名经常动态变化,这个时候为每个域名新增网站配置的工作量将会很大,可以通过节点默认配置来快速实现防护需求。
节点默认配置是指定一个JXWAF节点,当请求经过该节点时,会先匹配网站域名配置,匹配不到的时候,正常是会返回404,而新增节点默认配置后,会将所有未匹配的域名,都通过节点默认配置的设置进行防护和回源。
# 版本要求
jxwaf节点版本 >= 4.3
# 配置说明
JXWAF控制台 -> 运营中心-> 节点状态
查看节点对应的UUID,如图
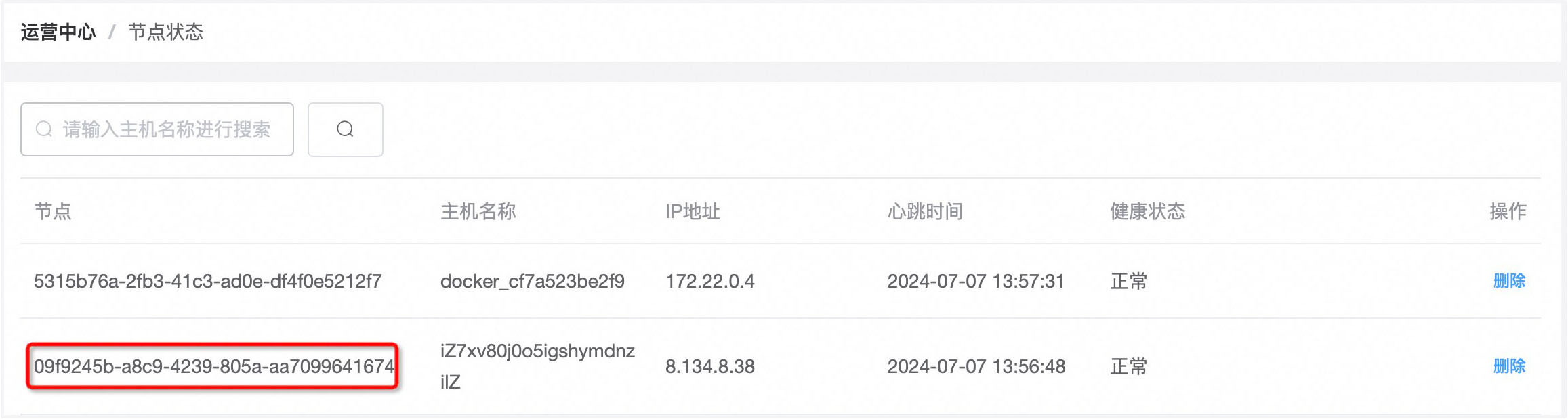
可以看到当前存在两个节点 5315b76a-2fb3-41c3-ad0e-df4f0e5212f7 和 09f9245b-a8c9-4239-805a-aa7099641674
本次我们需要为节点09f9245b-a8c9-4239-805a-aa7099641674开启默认配置
假设业务服务器地址为1.1.1.1,端口为8080,回源协议为HTTP,则配置如下:
JXWAF控制台 -> 防护管理 -> 网站防护 -> 新建网站

如果开启HTTPS,则需要通配符SSL证书,配置如下:

如果是两个不同的域名,例如 a.com 和 b.com,则需要配置两个节点的默认配置,分别设置 SSL证书为 *.a.com和 *.b.com
← 组件分享